Create Engineering Change Orders (ECOs) to track design changes and manage major versions. Release designs through an approval process that brings together key stakeholders
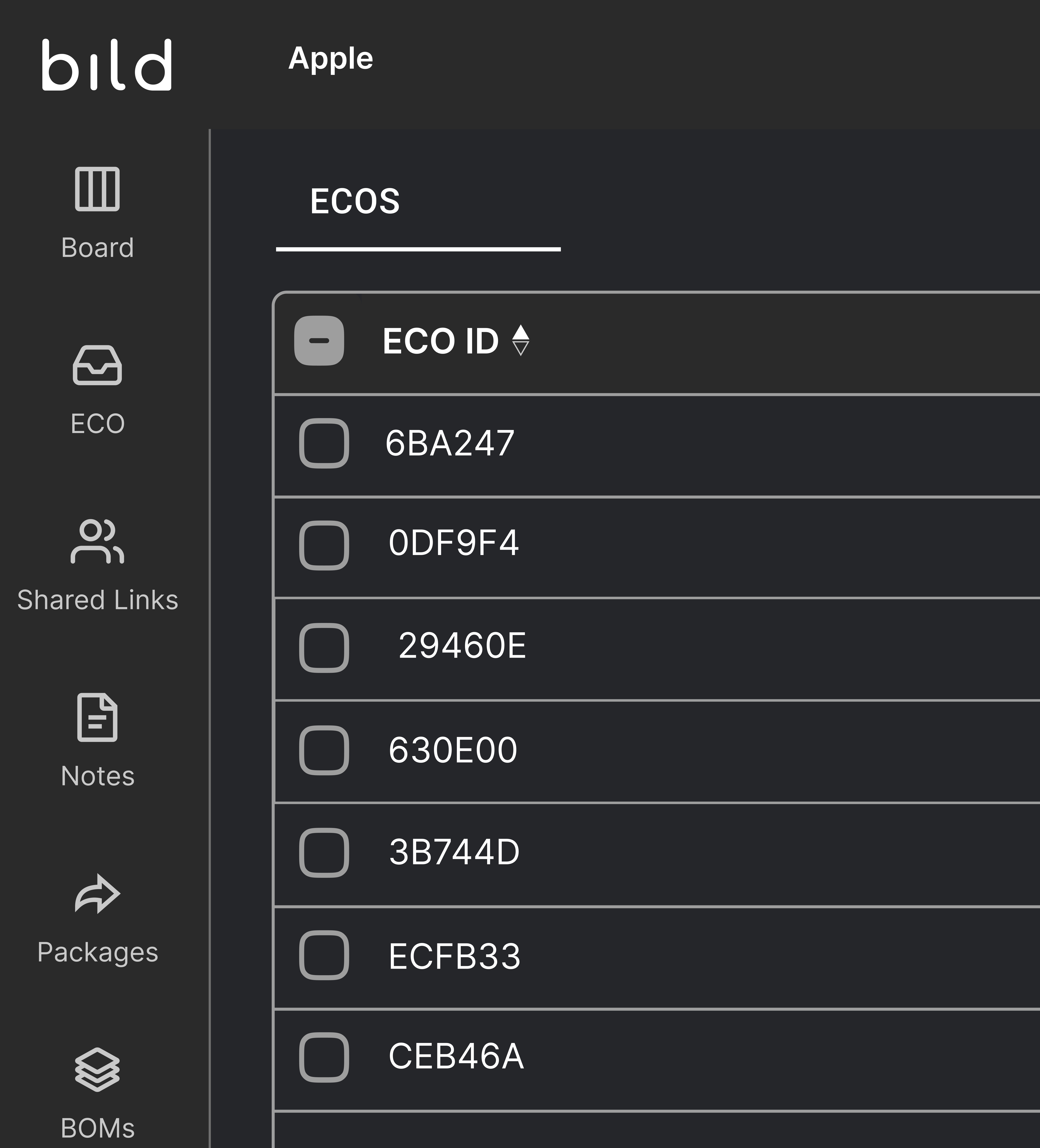
Process driven changes ensure accuracy and remove risk from the development cycle. ECOs capture a group of versions and roll up to a major release
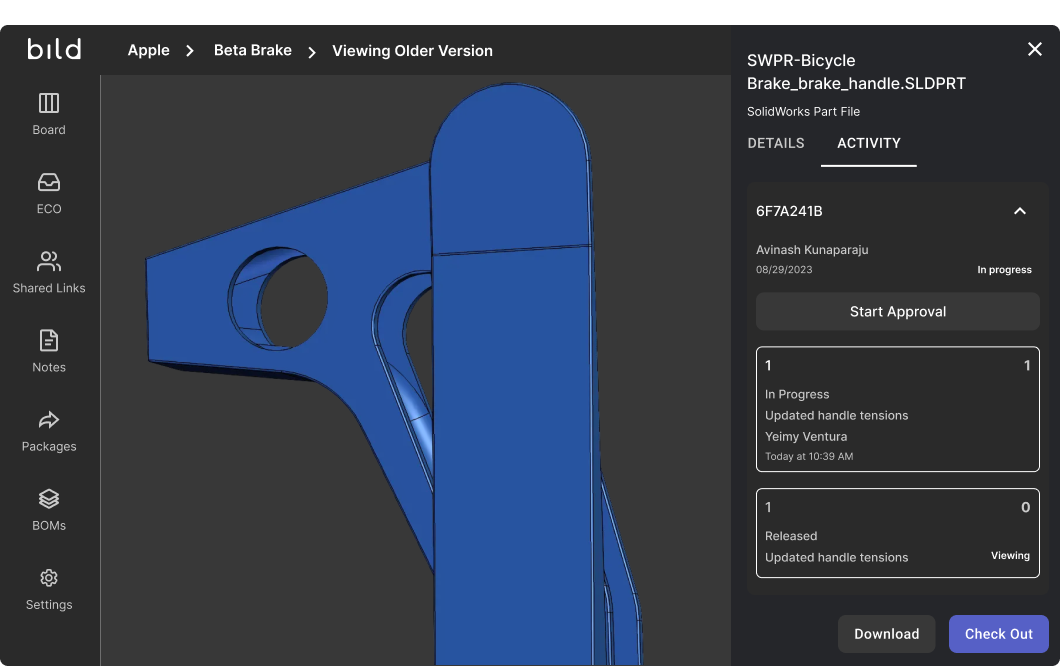
Request approvals from collaborators before releasing designs. Receive feedback from reviewers and tie them to ECOs
Ensure everyone is looking at the same design version
Lock designs during the approval process
Set custom workflows across different team members
Empowering teams to build smarter, faster, and together.


Yes, approvals are built into change orders in Bild. You can configure custom approval stages and assign reviewers from different departments such as engineering, operations, or management. Each approver can be set as required or optional, ensuring the correct stakeholders review design changes before release.
Yes, users with viewer access can still participate in approval workflows for ECOs and BOMs. This allows teams to involve stakeholders in the change management process without granting full editing permissions.
Yes, Bild supports automated change management workflows through configurable workflow rules. Administrators can automatically create ECOs, assign approvals, or trigger processes based on specific actions such as file uploads, revision updates, or metadata conditions.
Yes, when adding an assembly to a change order you have the option to include all of the children parts into the change order to be reviewed. Alternatively, when you release the assembly, you will have the option to automatically release and up-rev the children files with it.
Yes, in Bild, files associated with a change order that has an In Review status are automatically locked. This prevents users from checking out or modifying CAD files during the approval process, ensuring that design revisions remain controlled and traceable until the change is approved or cancelled.
Yes, Bild can automatically generate universal file formats when a design is released. For example, the system can create formats such as STEP, PDF, or other neutral CAD formats, allowing teams to easily share manufacturing-ready files directly from the ECO.
Bild ensures ITAR and ISO compliance by combining a U.S.-based secure infrastructure with automated audit trails. For ECOs, the platform can provide dedicated ITAR environments, ISO-ready traceability, granular access control, and digital signatures.