Drive collaboration across suppliers and vendors by seamlessly sharing versioned designs with them. Receive documents and DFM in a centralized portal
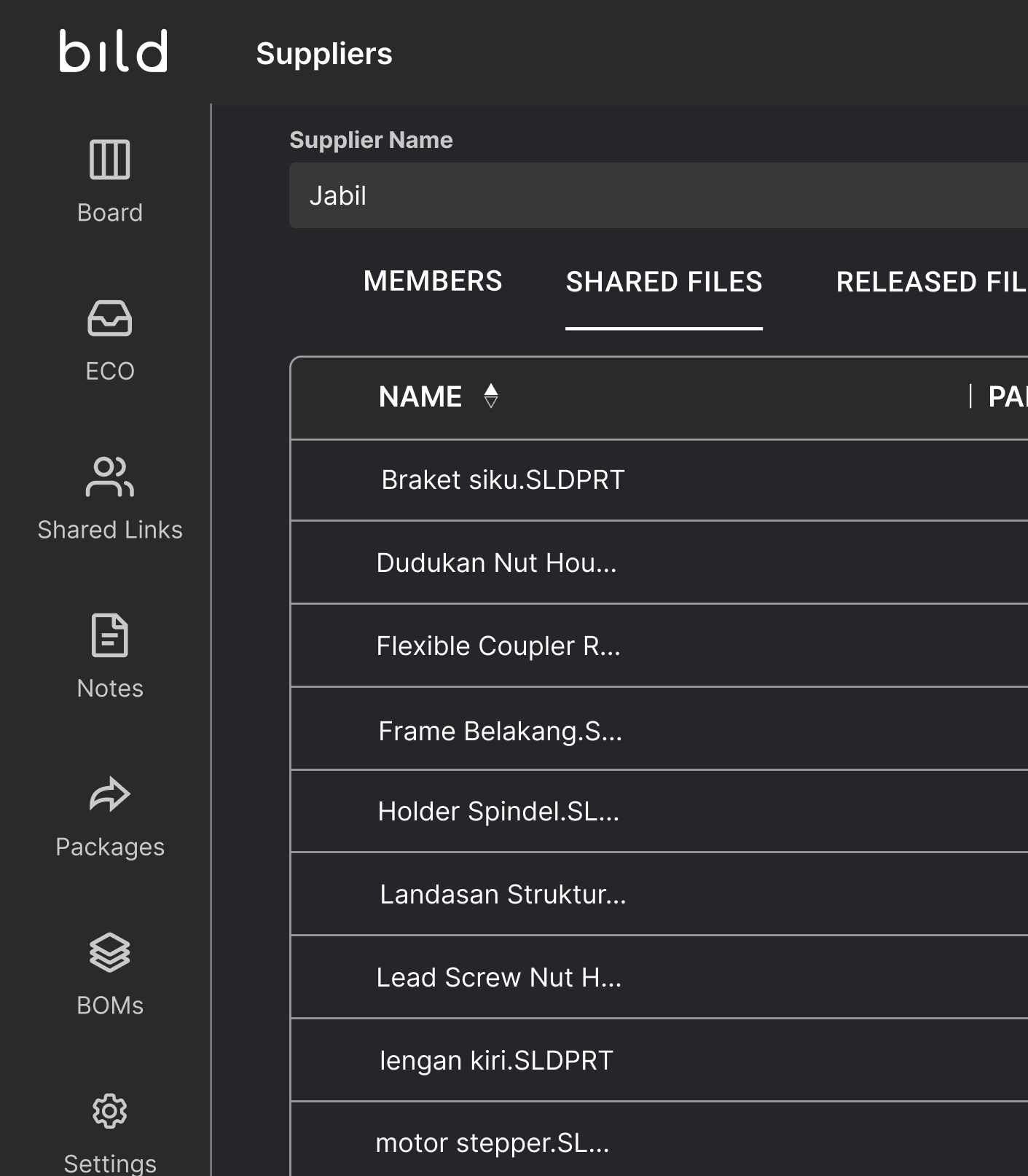
Suppliers receive information they are shared, and can share documentation back
Suppliers only see data they share, creating walls between suppliers
Easily see which designs are being shared to a specific supplier and which suppliers have access to a specific design
Add and manage alternate suppliers
Empowering teams to build smarter, faster, and together.


You can share any file stored in your Bild vault with suppliers, including CAD files, drawings, PDFs, and technical documentation. When sharing files through the Bild Supplier Portal, you control whether suppliers can view files in the built-in 3D viewer or download native CAD formats or universal formats. You can also choose to share the latest working version or only the latest released version of a design.
Yes. You can update supplier permissions at any time in the Bild Supplier Portal. This includes removing files to revoke access or adjusting whether suppliers can download native CAD files, universal formats, or only view files.
Yes. The Supplier Portal is a two-way portal where suppliers can upload and share files directly back to your team.
Supplier access in Bild is private and isolated. Suppliers cannot see other supplier groups, projects, or shared files outside of what you explicitly grant them access to.
No. Suppliers do not need a CAD license to view files shared through the Bild Supplier Portal. They can open designs directly in the built-in 3D viewer, where they can explode assemblies, take measurements, and view cross-sections.